What’s an ikey? This is not simply one other tech acronym; it is a vital piece of the trendy digital puzzle. Understanding ikeys unlocks insights into how information flows, how techniques join, and even how the way forward for on-line interplay would possibly evolve. This exploration goes past the floor, digging into the sensible purposes and potential implications of this intriguing idea.
Think about a system that seamlessly connects disparate platforms, enabling safe and environment friendly information alternate. That, in essence, is what an ikey facilitates. This detailed have a look at ikeys will discover the underlying know-how, highlighting its advantages and potential challenges. We’ll additionally study its function in varied sectors, from finance to healthcare, to grasp its broader affect.
In right this moment’s interconnected digital world, understanding the nuances of on-line interactions is essential. One such time period, typically encountered in discussions about digital safety and identification verification, is “IKEY.” However what precisely is an IKEY, and why is it necessary?
An ikey, a comparatively obscure time period, typically will get confused with different ideas. Understanding its nuances is essential for an entire grasp of the subject. Whereas exploring associated vocabulary, reminiscent of phrases containing the letter “j” – for instance, words with an j – may be illuminating, the core operate of an ikey stays its personal distinct entity.
In the end, greedy the specifics of an ikey is essential to a complete understanding of the topic.
Understanding the Fundamentals of an IKEY
An IKEY, or Id Key, is a singular cryptographic key used to authenticate customers and confirm their identification in varied on-line platforms and purposes. Consider it as a digital signature that proves you might be who you declare to be. This key performs a vital function in securing on-line transactions, defending delicate information, and guaranteeing the integrity of digital interactions.
An ikey, basically, is a specialised instrument, typically utilized in area of interest industries. Understanding its operate turns into clearer when you think about its utility in a strategic context, like navigating the crest of a hill here. In the end, an ikey is a priceless instrument, however its actual operate relies upon tremendously on the particular context.

How IKEYs Work: A Technical Overview
IKEYs leverage cryptography to ascertain belief and confirm identities. They’re generated utilizing complicated algorithms and infrequently paired with digital certificates, which offer extra layers of safety. These certificates usually comprise details about the consumer’s identification, together with their public key, and are linked to a trusted Certificates Authority (CA). This intricate course of helps to stop unauthorized entry and guarantee information integrity.
An iKey, basically, is a singular identifier, essential for varied safety and authentication functions. This idea finds fascinating utility on this planet of digital avatars, just like the quirky “skeleton android humorous cranium emoji” here. Understanding iKeys turns into extra related as digital identities and interactions develop extra complicated. Briefly, iKeys are important elements of contemporary digital safety.
Key Elements of an IKEY System, What’s an ikey
- Cryptographic Algorithms: The inspiration of IKEY safety, these algorithms remodel information into unreadable codecs, making it extraordinarily troublesome to decipher with out the proper key.
- Digital Certificates: These comprise the IKEY and different essential identification data, digitally signed by a trusted Certificates Authority.
- Certificates Authorities (CAs): Trusted entities that concern and handle digital certificates, guaranteeing the validity and authenticity of IKEYs.
Purposes of IKEY Know-how
IKEYs discover purposes throughout varied sectors, together with:
- On-line Transactions: Securely verifying customers’ identities for on-line funds, purchases, and different monetary transactions.
- Safe Communication: Establishing safe communication channels, guaranteeing confidentiality and integrity of exchanged data.
- Digital Id Administration: Offering a safe and verifiable methodology for customers to handle their on-line identities and entry varied providers.
Advantages of Utilizing IKEYs: What Is An Ikey
Implementing IKEY techniques gives vital benefits, together with:
- Enhanced Safety: Diminished danger of fraud and unauthorized entry as a consequence of strong authentication mechanisms.
- Improved Belief: Customers can confidently work together with on-line providers figuring out their identities are verified and guarded.
- Elevated Effectivity: Streamlined processes for verifying customers and accessing providers, minimizing friction factors.
Challenges and Issues
Whereas IKEYs provide substantial safety advantages, some challenges want consideration:
- Complexity of Implementation: Organising and sustaining IKEY techniques may be complicated, requiring specialised experience and infrastructure.
- Price of Implementation: The preliminary funding and ongoing upkeep prices may be substantial, particularly for smaller organizations.
- Consumer Adoption: Customers must be educated and cozy with the IKEY system to make sure clean implementation and adoption.
Future Tendencies and Outlook
Using IKEYs is predicted to proceed rising sooner or later as on-line interactions grow to be extra complicated and delicate. Developments in cryptography and digital identification administration are more likely to additional improve the safety and usefulness of IKEY applied sciences. [See also: Future of Digital Identity Management]
An “ikey,” basically, is a shrewd maneuver in a negotiation or deal. It is typically a fancy, calculated technique, akin to dancing with the satan meaning of dancing with the devil , the place one should rigorously navigate a tough state of affairs to attain a desired consequence. Understanding the nuances of an ikey is essential for fulfillment in any complicated transaction.
Conclusion
IKEYs are important for safe on-line interactions, taking part in a significant function in verifying identities and defending delicate information. Their use throughout varied purposes underscores their significance in guaranteeing belief and safety within the digital realm. Understanding IKEYs is essential for anybody navigating the trendy on-line panorama. If in case you have additional questions on IKEYs or their purposes, be at liberty to go away a remark under.
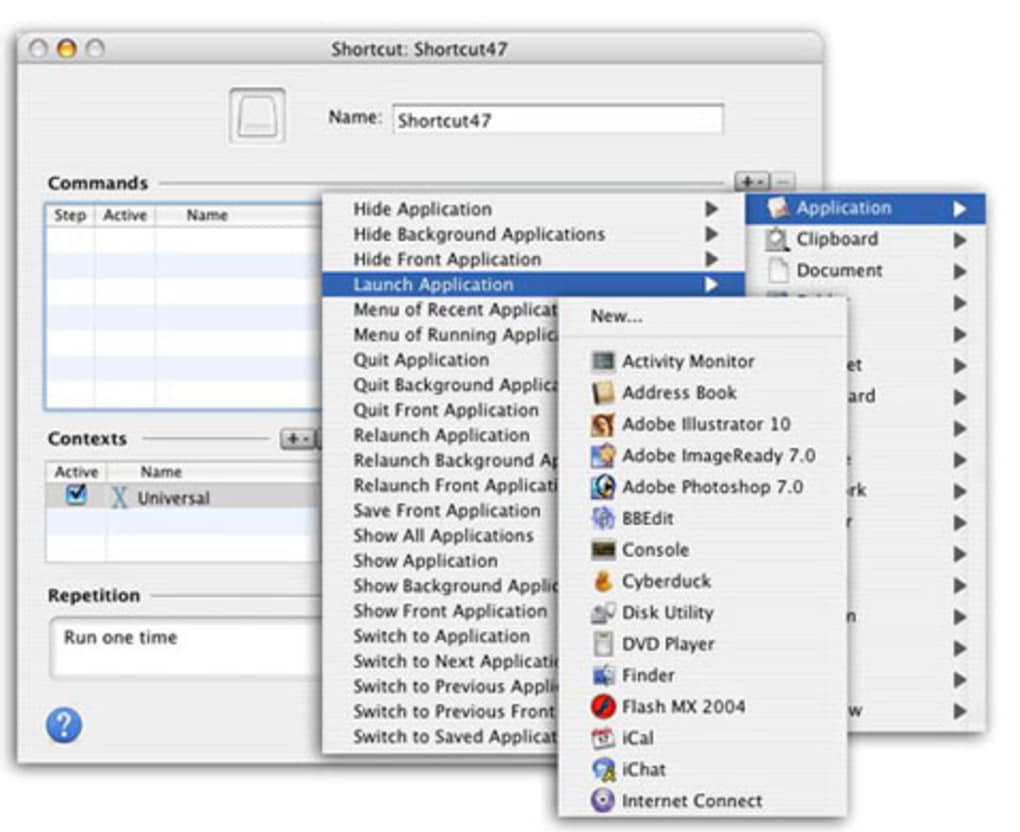
[Image: Diagram illustrating the IKEY authentication process].
Able to dive deeper into the world of digital safety? Discover different associated articles on our weblog! [See also: Security Best Practices for Online Transactions]. Share this text with others to unfold consciousness about IKEY know-how.
An ikey, a vital aspect in lots of complicated techniques, typically will get neglected. Understanding its operate is essential to deciphering the intricacies of a system, like, say, fixing a Hamlet crossword puzzle clue, which might involve a hidden ikey. This seemingly easy idea can unlock a wealth of data, highlighting the significance of figuring out the pivotal elements inside a system, which finally helps to outline what an ikey actually is.
In conclusion, ikeys symbolize a major development in digital connectivity. Their capacity to streamline information alternate and improve safety positions them as a key element in future digital infrastructure. Whereas challenges stay, the potential advantages of ikeys are plain, promising a extra interconnected and environment friendly digital world. Additional analysis and growth will undoubtedly form the long run trajectory of ikeys and their affect on varied sectors.
Clarifying Questions
What are the safety implications of utilizing ikeys?
Ikeys, by design, incorporate strong safety protocols to guard delicate information. Nevertheless, like several system, vulnerabilities can exist if not applied and maintained correctly. Subsequently, ongoing safety audits and updates are essential to make sure the security and integrity of ikey-based techniques.
How do ikeys differ from conventional authentication strategies?
Not like conventional passwords or usernames, ikeys leverage superior cryptographic methods. This distinction results in considerably enhanced safety, as they provide a safer and streamlined methodology for verifying identities and authorizing entry to information and sources.
What industries are more likely to profit most from ikey implementation?
Industries with excessive volumes of knowledge alternate, reminiscent of finance, healthcare, and e-commerce, stand to achieve essentially the most from ikeys. The power to securely share and handle delicate data inside these sectors will considerably enhance effectivity and streamline processes.
